Cloud Computing (INF 101)
the cloud cloud computing computation maths physics evolution immortality artificial intelligence brain integration
The cloud and beyond
The Cloud is an interesting and peculiar concept, as the cloud employs information technology and its advancements, and then integrates them with real-time updating, backups and documenting of an array of things. In this brief dissertation, cloud computing and its future’ (application, and implication) will be discussed; the ideological wonders and splendor that is incurred will be explained, and the framework behind the cloud’s very existential state will be heavily disseminated upon.
Here now, will I describe the attritional beneficence of cloud-computing.
575]· Origins
575]· Ethicality of brain-integration respective of subjective moral basicity, and objective moral febricity of religiosity
575]· Chappie and its’ filmographic implications
575]· ‘Light years’ ahead –
575]· Financial, corporate, militaristic, governmental and social implications of cloud-computing
575]· Is the next step of evolution integration with the cloud?
575]· Reinforced thesis (and summarized conclusion & ending)
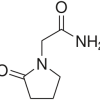
Cloud computing (in specificity and layman’s) is a hosting mechanism designed by utilization of radio frequency (Rf) for the purposeful reasoning of backing up one’s documents, media files, and also for the securing and placement (secondarily) of one’s copyright protected materials, as well personal information relating to medical, biologic, physical, legal and academic/governmental.
The cloud backs its data onto machines called servers, and their primary purpose is for hosting (domains, websites, file backups, applications and various media contents) on its database of intranet-based connectivity and relay. Servers often times work together to maximize computational power, speed, concision and overall efficacy (Bowles, 2010 – chapter 9.4: The Clouds Are Here, para 6.24.,) corporations such as google, amazon, apple – with outsourced venues and engines, various collaborates, governmental affiliates and brokers, investors and even federal and militaristic levels of hierarchal classification and corroborations utilize these such servers in massive groupings for maximized usage of data-storage (cloud storage;)
further, and by means of uploading the unclassified, and/or classified documentations to cloud sources such as (iCloud, Microsoft SkyDrive, or other individualistic third party providers of server-hosting manufacturers like Dropbox) who have contractual obligations with individuals, parties, businesses, commercial businesses, corporations and governmental agencies for file hosting and backup services.
Though, in many cases – servers are bought and used under intranet (secured) settings and atmospheres such as militaristic bases, or places of governmental significance eg., the Pentagon, effectively allowing closed-system (intranet-based) exclusive rights, ownership and proprietary asset to a documentation(s) rightful owners regardless of file class or type – storing all such aforementioned contents on purchases and personalized secured servers for the sake of national security, technological continuance and social-construing assurance.
In regard to additional venues of data-collection and storage, satellites are used and utilized by top-bidding or paying persons, businesses, corporations, government powers or wealthy people – giving maximum accessibility, stability and procurement/ascertainment and reachability (with peace of mind for security of documentations) of one’s cloud-stored contents, being nothing more than photonic remnants of Rf-based matter, being simply immaterial subatomic microcosms, hence nanotechnology’s basis for technological existence and frameworks – and all of the digitalized material (contents of all sorts) are compressed, encrypted and scrambled into tiny Rf parcels found within miniscule sectors of the satellites, and/or servers – thusly effectually allotting the tremendous possibility for storage and performance.
How it all works – cyclic continuances
Stars – living dead and forming all alike create electromagnetic atomicity, which creates with (Kelvin-scaled temperature) proper atmosphere, photonic atoms to which are microcosmic in scaling. Those photonic atoms travel at precisely 186,000 or C2 which is measured by astronomical units < light years which translates to how long it takes a beam or array of light to travel lineally for a year in constancy – which support the mathematical structure of light speed and electromagnetic components.
Furthermore, black holes are measured by means of particle collision and acceleration – as they are mimicked successfully, a physical constant named ‘Hawking Radiation’” (Mlodinow & Hawking, 2010) is effectually applied to the atomized collision – depicting concisely what a black hole is, and does as such is nothing more than a cosmic vacuum, which forcefully with use of gravitons working at relativistic speediness, likened to light speed envelop and pull in electromagnetically photons and other cosmic particles – working as a naturalistic albeit astronomical vacuum cleaner, keeping clean and soundly secure in stability, the cosmos at large – for every sun that dies goes supernova (and in time, our own sun will too) a black hole is formed, enveloping all light…in ironic demeanor;
Moreover, black holes possess such immense amounts of compressed light, that it is compacted quite literally into envelopment and consequential oblivion by means of self-deconstruction through which the envelopment continues until the point of becoming unphysically manifest – being immaterial and subsequently rematerializing dimensionally as a multiversal (multiverse-universe) component for the formation of another star – which fuels the varied energies needed for the formation of a constellation, then galaxy, then solar system and life.
As such a process is indisputably complex, the same is applied on much more complexly scaled levels of systemic formulization – via macrocosm and microcosmic biologics – fueling various fossil fuels, which effectuate vegetation that in turn substantiate physically existential life.
In this same demeanor, gravity (G/R) and light (photons) are the binding forces which allow the biological species to become self-conscious, with five different though specific senses to which allow lifeforms (Mammaliaformes) to see and hear, taste, feel and touch with dispensable appendages for the sake of procreation by natural selection (and selective genomic proliferation) by process of eliminatory deviation, allowing mammalians and other lifeforms to consummate, procreate and spread their genetic antiquities and oddities onto offspring – essentially repeating the cyclic process for which a person lives and dies.
However, and though this process seems to only better parts of that person’s gene(pool) which are spread unto children, effectively allowing the essence of an individual’s collective unconscious (or conscience collectivization) to live on infinitely – lest the blight of involuntary death occurs, and kills remaining gene pool recipients and progenitors, for which would revoke or remove in totalistic entirety the unique set of microbiologic atomicity (chemistry) per persona, genera, species genus and individualistic thought pattern.
And in this same demeanor, batteries power computers – and computers power (and host) applications which allow cloud-computing to exist in a state whereas we can interact and effectively communicate with such an abstraction such as electricity and/or electromagnetism in generality. Thus, this race has begun to technological superiority by means of innovative human interface device(s) creation.
Moving on, in general, cloud technology is lavishly and enigmatically high class technological standardization, as it is new, evolving, interesting and stupendously useful, powerful, performing and optimal for computational preference and continuance.
According to this source, there is much more good than there is detrimental in cloud computing – and with that I agree; what is change in essentiality, for what is betterment and furtherance without risk? There would be no progress without risk of repercussion(s).
“Cloud services are indeed usually much cheaper than their dedicated counterparts. Administration and management oversight are simpler under a single, central authority.’ Small businesses and startups have taken advantage, using low-cost cloud services during their first few years.
Cloud platforms are critical avenues to getting started for many companies, giving them access to many customers at low cost. Many business leaders see the cloud as an engine for small businesses and job creation.’ Cloud storage services are also a boon for individual users, most of whom do not back up their computers and mobile devices regularly or at all. Cheap, automatic backup to cloud storage protects their valuable data from loss. (Neumann, COMMUNICATIONS OF THE ACM, 2014).’”
However, as aforementioned, there are always repercussions or negations to every aspect of things, and cloud computing is not without exception. According to (Asal, Ardagna, Damiani, & Quang, 2015).”There are risks to this modernized, more impersonal technological transition…
“Cloud computing supports a vision of IT where resources and services are provided on demand on a pay-as-you-go basis [Armbrust et al. 2009, 2010].’ “It provides infrastructure, platform, and software services—known as IaaS, PaaS, and SaaS, respectively [Mell and Grance 2011]—lowering the effort needed to manage computational infrastructures.’ “Experience has shown that the cloud can make IT cheaper, simpler, flexible, and accessible to everyone without requiring the expertise needed to own, operate, and manage traditional on-premises systems.”
“Cloud customers are free to focus on service development, while cloud providers can concentrate on management activities providing an infrastructure that gives to customers the illusion of the availability of infinite resources [Ardagna et al. 2012].’”
“Gruschka and Iacono [2009] present a weakness in the SOAP-based control service of Amazon EC2 against signature wrapping attacks, originally described in McIntosh and Austel [2005]. The attacker was able to modify an eavesdropped message faking the digital signature checking algorithm and executed commands on behalf of legitimate users. Jensen et al.’ [2009] present security issues in cloud computing, considering XML signature, browser security, cloud integrity, and flooding attacks.”
In addition to the preceding…“They also introduce the cloud malware injection attack, where a malicious user tries to add a malicious service implementation and confuse the cloud provider by letting it consider the malicious service as a normal one. Somorovsky et al.’ [2011] test the security of the cloud control interfaces of Amazon public cloud and of a private cloud based on Eucalyptus. The results show that in both cases the control interfaces can be compromised by means ACM Computing Surveys, Vol. 48, No. 1, Article 2, Publication date: July 2015.”
“From Security to Assurance in the Cloud: A Survey 2:7 of signature wrapping attacks. The authors propose a novel methodology for the analysis of public cloud interfaces and discuss possible countermeasures to the identified attacks. Chonka et al.’ [2011] focus on two attacks that can target the cloud, namely HTTP Denial of Service and XML-based Denial of Service [Srivatsa and Iyengar 2011]. In particular, they recreate the above attacks, present a solution to identify the source of an attack, and introduce an approach (Cloud Protector) to detect and filter these attacks (Asal, Ardagna, Damiani, & Quang, 2015).”
The aforementioned testation is significant as cloud computing is quite literally taking over how technology works – and even evolves. Of course security protocol will always have flaws – as the future is merely predictable (by implicative considerations) though it is still unknowable absolutely, thus uncertainty and humanity coincide and perfection does not exist without some metaphor of forfeiture. For instance, citing referentially from memory, I do recall iCloud being hacked, just as google pays anyone a considerable sum of money if they are able to hack their updated XML/Java designations (done biyearly in Seattle, WA.) Similarly, the hacking of iCloud (and thankfully, it was exclusive in incidental happening, as an infamous person was hacked by a teenager for no reason other than boredom) and because of this signifying experience, Apple has improved its security standards tremendously, henceforward the innovative foundation of the iPhone 6 Plus and Retina/DNA scanning technology, and cloud-based encryption reformation.
The beneficence of cloud-based computing and similar technological componentry far outweigh any detriment (I think) as things will always be found to have a glitch or error in some part – as computers are formulated by fallible and incredulously intangible human beings, thus impracticality and illogic, and/or conversely…mathematical construct will have a point of failure and forfeiture – due to human error; moreover, when a perfected artificial intelligence begins formulating computational devices, and a real-life Skynet is borne, then humankind will truly have mastered the self – by means of forced evolution of our species.
In this context, human-to-computer brain integration will most likely be possible in the nearing future, however – until we’ve mastered security protocol, brain-integration via cloud computing is simply too dangerous – as humankind is invariantly odd in moralistic dilemma. In this sense, humankind has not one collectivized and accepted set of standardized rules, conditionings and laws to abide by – but rather subjectivism in surrealistic motivation; we’ve individualistic thought patterning, and because of our indifference and uniqueness and sense of self, we’re unruly, undeterminable, unknowably unpredictable and thusly – we cannot be trusted not to manipulate and cheat others by ‘hacking’ and extorting others by manipulation of their brain firmware-integrated cloud-computation. Just to note, if I were one of the firsts to complete this brain-integration, I would definitely use the term ‘brain-ware.’”
And within thoughtful essence, it’s unclear as recently implied, where the future will take us in individualistic demeanor (in regard to journey) however, in order to better ourselves (as history teaches) we must take risks, we must be encouraged and adventurous, willing and daring in our pursuits and endless endeavors if ever we wish to further ourselves individually, and collectively in sociality.
There was a lot more I had wished to add, but they are of personal works and scientific avenues of consistent pursuit and variant researches, and such would only be applicable in testimonial dissertation for a graduate, or mastering thesis paper – and alas, I am not to such a point yet…though I’m a studying ethologist (which is evolutionary psychology) and have lots of knowledge within the biologics and naturalistic things such as evolution, anthropological variations, anthropomorphism, psychophysiology, and for recreational sport – quantum physics (and the study of light), I am not a certified or officiated expert by any such means of annunciated affiliation, thus I cannot include my works – as they are without scientifically necessitated requirements – being that of peer review, demonstration and testability-status. If ever you’ve seen the film ‘Chappie,’ or if you have not for that matter – I highly recommend it, and for the sake of your intellectualistic curiosity, I am working on an assimilar mode of scientific assignment.
In closing, it’s not possible to speak from a subjectively-objective perspective, such is individuality and humankind in essence – making us rather unique in arbitrary rendition; in that, I say that irrespective of religiosity and all subsequent belief systems, or moral values, I cannot say that the pursuit of transhumanism-related theory such as robotics and artificial intelligence (AI) foundation is unethical or perfectly moral – as one would first need dictate with absolute knowledge and understandability on if there is, absolutely and objectively by falsifiable verifiability a (gods) and then second, consider on if a god can exist if a ‘soul’ doesn’t exist, from what I understand of rabbinical texts and through my interpretations, it seems that much of science simply cannot coincide with religiosity – as much religiosity is emphatically based upon the conceptuality-in foundation of faith, whereas most science is concrete, palpable and demonstrable in scientific methodology.
Therefore then, from my perspective, there is either one or none of the following: a consciousness (a Darwinian-based brain) if you will, or a soul (a spiritualistic abstraction that grants freewill and dictation as well as decipherability and inheritable constraint, restraint and discernment.) In summary, if brain integration is ever to be possible, and then achieved – one must possess a consciousness (with carbon, or Darwinian based existence), thus the metaphorical terminology for the complexity of the brain-mechanism termed ‘mind’ can be transferred from mortal coil to computer or robotic construct.
Further, and conversely, I’m under the distinct impression and indiscernible belief that a rabbinical-basis, or spiritually acclaimed and based concept such as the ‘soul’ would not be transferrable as that would defy a (gods) conceptual framework, ideological principles and defeat and contradict any purpose for meaning in human existence (from spiritual perspective) and then the concept of freewill would be forlornly recanted, as such biblical notions would be voided, absolutely and immutably, at least in my mind which – may or may not seem logical to my reader(s).
And thusly in closing, I’d like to state for the sake of affirmation, that I am impressively aspired by cloud computing – it awes me in wondrous and dismal thoughts in and of the (seemingly) endless possibilities, and scenarios that would be eventuated one way or another, if something can happen – it will happen (Murphy’s Law).
I’m all for technological innovation – after all, I’m aspiring to become a leading innovative figure within my generation as is, and it would be shamefully appalling to deny facts such as scientific forwarding and advancements when such is obvious and apparent to anyone with eyes to see and a mind to think with – I believe there are risks…but hacking has been around for a while now – and as mentioned at the (Defcon technology biannual meetings) which consists of technology experts, investors, entrepreneurs and enthusiasts, geeks, nerds and other ‘trekkies…’
Further (continued) meet and discuss important things within information technology such as (especially significant) security protocol, and vulnerability, additively to innovations and new technologies – in year 2007’s Defcon convention, talk persons hacking pacemakers was discussed – and in 2012, talks of people hacking emergency service phone lines, computers, alert systems, light systems and geocaching/triangulation technologies for pranking, or other cruelly sickly depravity were controversially debated upon.
And though many hackers do what they do for the sake of profit, or for the sake of improving overall security protocol – there are psychopaths and sociopaths both that exist (and reside within the hacker’s underground world) thus evil acts will always be enacted upon, as there will always be shootings, murders, cruel pranks and bullying/harassment – such is incomprehensibly unsolvable and intangibly undefeatable in moralistic dilemma, as we can predict (as mentioned earlier) but know with absolute certainty, we cannot – and that is what makes us unique, good and bad – capacity for good and evil; more, and though such capacity lays dormant within all of us – we have the ability to discern, decipher and consider our thoughts before they become actions – thusly enabling even the criminally insane to live freely without persecution for their thoughts – but only sought and punished for their indecency found within their heinous actions and enactments or emanations of such darkly thought considerations.
In the endings of all things, peace will never be harmonically stabilized and perfected – as madness, depravity, cruelty and sorrow still exist – as happiness, ignorance shallow regard and antipathy exist – so also does the human spirit exist, to which essentially makes humankind…human, and like it or not – without our unique capacity for the capability of doing good things, or for committing evil both are necessary for conscience and conscious thought – for conscientiousness to exist, for good to exist – opposites must also exist, as light exists so surely does its antithesis, which is the absence of light – darkness.
REFERENCES
(Bowles, 2010) Introduction to Digital Literacy, Chapter 9.4: The Clouds Are Here)
Claudio A. Ardagna, Rasool Asal, Ernesto Damiani, and Quang Hieu Vu. 2015. from security to assurance in the cloud: A survey. ACM Comput. Surv. 48, 1, Article 2 (July 2015), 50 pages, p 1-13. DOI: http://dx.doi.org/10.1145/2767005
Davis, M. (2000). The universal computer: The road from Leibniz to Turing. New York, NY: Norton
(Hawking & Mlodinow, 2010: The Grand Design., a briefer time of history)
ICCI (Conference), Pan, J. S., Chen, S. M., & Nguyen, N. T. (2010). Computational collective intelligence: Technologies and applications: Secondinternational conference, ICCI 2010, Kaohsiung, Taiwan, November 10–12, 2010, proceedings. Berlin: Springer.
(Neumann, COMMUNICATIONS OF THE ACM, 2014, Vol. 57, Edition 10: pages 24-28)
I hope sincerely, in the profoundest worrisome plea, that this paper was satisfactory for assignment requirements.
Thank you for a great class and fun (and informative) assignments,
Dearly, Sincerely,
Jacob A. Eder;
All Rights Reserved; 2011-2015; copyright protected:
(T3T Innovations); Jacob A. Eder; Darkly Origins/Eerie Flickering;